What is Shodan
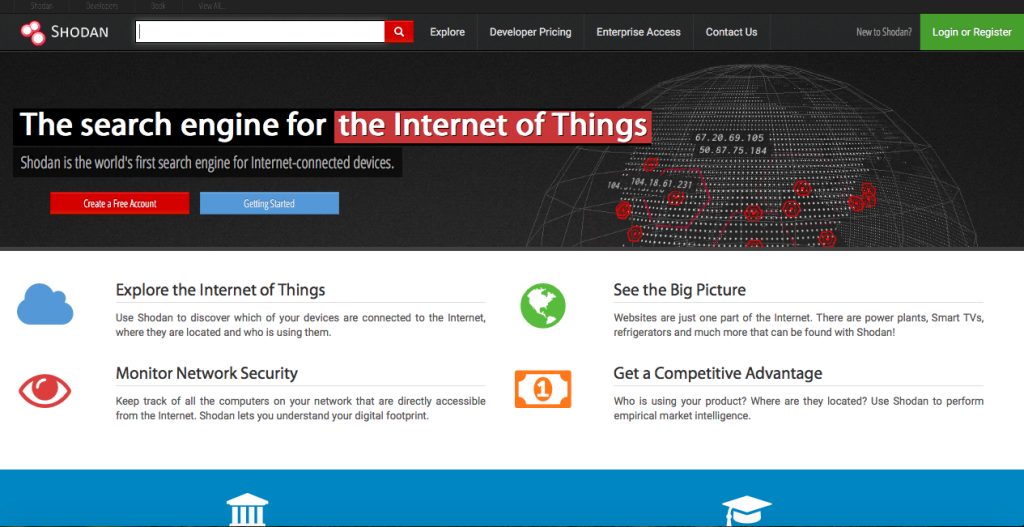
Shodan was created by computer scientist John Matherly as a hobby. Matherly wanted to track any type of device connected to the internet. This is how Shodan became real in 2009.
Shodan indexation works by searching open ports of any service or device. This means that Shodan, unlike any normal search engine, does not focus on searching web pages but on collecting the banners of the services (server response to a request). These services include HTTP, HTTPS, FTP, SSH, Telnet, SNMP and SIP protocols. Then, the user can search for devices by regions or geographic areas applying Shodan filters.
What is possible to find with Shodan
Well, almost everything! And this is the scary part of Shodan. That is one of the reasons why vice.com calls it the most dangerous search engine in the world. Shodan is able to find from a smartphone to a refrigerator, a security camera system, and even a nuclear plant.
Shodan is a specialist in scanning the internet of things. However, when Shodan performs a deeper search, it gives back results with information such as what type of device is connected to the internet, where is located and who uses it.
Shodan can find from a refrigerator to a nuclear plant
In fact, with Shodan Maps, user can have satellite and street view of the places where the devices were found.
But Shodan is not that bad at all. Shodan website promotes the use of the search engine among medium and large companies. For instance, Shodan can help you do empirical market intelligence because it provides the information about those electronic products connected to the internet that people use the most. Shodan is also useful to monitor the computers of your network with internet access.
How Shodan works
Basically, Shodan tracks public access devices, preferably in SCADA systems (Supervisory Control and Data Acquisition). SCADA systems are used to control and supervise industrial processes remotely in real time.
Shodan uses automated search tools that allow massive queries. One of these tools is Shodan Diggity. This tool is powered by a database known as Shodan Hacking Database that works as a kind of dictionary to locate different devices connected to the internet: printers, webcams, routers, transit systems and, of course, industrial control systems.
Shodan´s danger
As mentioned earlier, Shodan can be good or bad, everything depends on the hands that control it. Unfortunately, Shodan still attractive to cybercriminals and hostile nations interested in activating a large-scale war similar to a cyber Blitzkrieg.
If Shodan is capable of tracking SCADA systems as we mentioned above, the national security of many countries could be compromised since an attack on their infrastructure is possible by using Shodan.
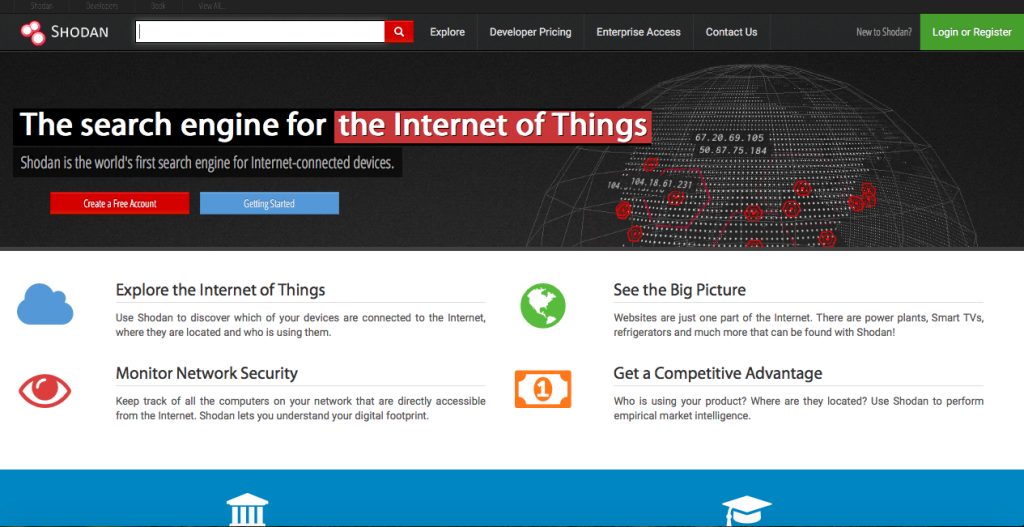
Currently, any user can get 10 results in an average search with Shodan. Registered users in the Shodan platform can obtain up to 50 results per search. To become a registered user you must pay a fee and explain the reasons why you want to use Shodan.