Log management and SIEM
The Key To A Secure Digital Environment
Get a comprehensive solution for log collection and management, analysis, evaluation, and security incident management. We will also tailor the infrastructure and log management configuration to your needs and ensure continuous event monitoring.
Why deal with log management and SIEM?
Do varianty s nadpisem vlevo by se hodil nějaký krátký perex…
Centralised log storage
Event logs from all infrastructure components, from network to applications, are centrally stored in a unified format, which provides complete control over all events.
Aggregated event management
You can revisit events at any time, examine them more closely, and discover connections that cannot be established when collecting logs separately in different locations.
Mitigate security risks
Continuous monitoring and a comprehensive view of the collected data enable better and more effective identification of vulnerabilities and security threats across servers and applications.
Legislation compliance
Log collection helps you to comply with GDPR and Cybersecurity Act requirements. With SIEM, you will be assessing events in accordance with the emerging NIS2 directive.
Services for event management
Log management
- The log management tool gathers logs from various platforms and stores them in a unified format in a central repository.
- You can access all relevant data, quickly search, correlate information, and subsequently pinpoint potential performance or security issues. We will set up the software and configure everything to your requirements.
SIEM
- SIEM (Security Information and Event Management) works on top of log management and primarily focuses on security.
- At this level, we set up fundamental rules for analysis, event correlation, and reporting, which you can expand and customise with alerting rules as required.
SOC
- SOC (Security Operations Center) consistently assesses potential incidents and addresses legitimate threats.
- Potential and previous incidents are handled with the assistance of our CSIRT team.
What you get with Log Management and SIEM
At MasterDC, we will design an event management solution precisely to your needs. This can encompass log collection (log management), which can be complemented with analysis and processing (SIEM) as well as a security operations center (SOC). We can also implement the tool on dedicated hardware or within a shared SaaS environment. The solution may include:
- Log collection at various levels (users, devices, applications, infrastructure, etc.).
- The configuration of event logging on a per-case basis.
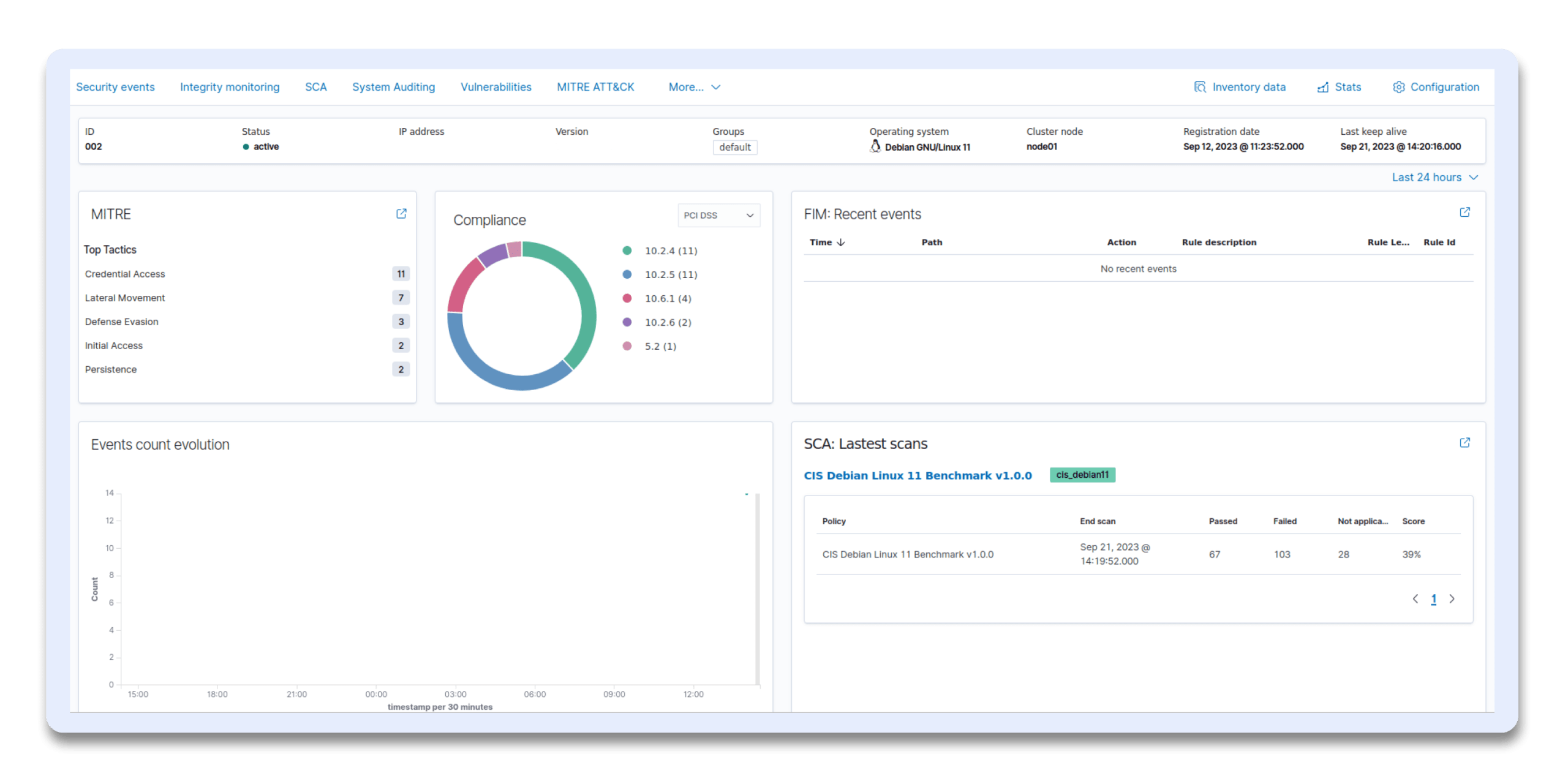
- The creation of dashboards with log visualisation.
- Log analysis.
- The establishment of alerts and a definition of processing.
- The identification of threats and vulnerabilities.
How it works
It starts with an analysis of your system.
We then implement tailor-made configurations.
Your solution is monitored 24/7.
Why choose us?
Your data security – our priority
We have been focusing on server security and protection for a long time, which is why our CSIRT team came into existence so that the information might be shared easily and, thus, attacks are prevented ASAP.
Three decades of experience
We launched at the time when Amazon was selling music, Google was registering its first domains, and the word Facebook was non-existent. Therefore, our extensive experience allows us to provide valuable insights and expertise to our clients and partners daily.
Two data centers for enhanced reliability
Two is better than one, and you will particularly appreciate that our data centers are located in both Prague and Brno when in need of a secondary location backup and/or when you are looking for another location for geocluster deployment.
Certified hardware only
Our services have been built on DELL-certified technologies. In addition, being the very first CSP partner in Czechia, we have access to hardware at a better price, which is also reflected in our services.
Connect with our team today to discuss your needs and schedule a meeting.
- +420 515 919 805
- sales@master.cz