System hardening removes and eliminates vulnerabilities and security gaps; its goal is to minimise the system’s attack surface.
Un-updated software and firmware versions, unencrypted network traffic, and the misconfiguration of ports, firewalls, switches, or other infrastructure components often spread attack surfaces. However, they can be reduced, for example, by regular updates, but also by making the system leaner overall, which means uninstalling unnecessary software and disabling some redundant services.
The reduction of security risks and vulnerabilities is primarily made to prevent potential cyber-attacks. Hardening also requires continuous work and regular reviews of the security level. However, the effort invested pays off many times over with the number of attacks repelled and data saved.
Why Even Go Into System Hardening?
The biggest motivation should be to increase cyber protection. The number of DDoS attacks continues to grow, and their strength has already reached 100 Gbps. However, systems are also threatened by malware, Basic Input-Output System (BIOS) vulnerabilities, and intrusions into internal networks.
Hardening a server or operating system includes additional benefits, mainly related to the reduction of tools and software mentioned above. In addition, less complicated systems face fewer operational problems and misconfigurations, and more compact, simplified environments are also easier to monitor and conduct regular security audits.
Hardening A Server In Four Steps
1. Determine the security level you want to achieve
For systems and servers where the security level has not yet been systematically addressed, you first need to establish a “baseline”. This baseline refers to the state of the operating system, server, or network you want to improve the security on.
2. Find out the ideal state by benchmarking
Benchmarking compares the system to official recommendations, e.g., from hardware manufacturers, specific software publishers, or cybersecurity institutions. Usually, rules and recommendations can be found with official software documentation, e.g., Microsoft Windows. However, more general documents are also issued by institutions that focus on whole areas, i.e., server or network security. An example is the benchmarks published by the US company CIS (Centre for Internet Security). However, there are many of these on the internet, which is why they vary in quality and content.
3. Identify problem areas in your system
Comparing your system to a benchmark will provide an overview of the areas with the biggest gaps. Then, based on this assessment, it will be possible to adjust the system’s configuration. However, sample benchmarks do not need to be filled in completely, as it always depends on the predetermined objectives and the riskiest system areas.
4. Check the system regularly and keep to the established baseline
The initial adjustment is just the beginning. The system needs to be constantly, or at least regularly, monitored and checked from time to time. These reviews will reveal any deviations from the ideal state (baseline) that can be corrected in time to strengthen the server’s or network’s resilience.
What If The System Is Too Complex For Manual Control?
Manual hardening of smaller infrastructures is not a problem. However, the process can take longer for larger ones that consist of several different components. It also requires the capacity of more people and naturally increases the risk of human error. For such cases, it is useful to take advantage of the available automatic system scanning tools, many of which are even open source. Nevertheless, for freely available versions, it is better to choose those that do not need to be installed on the server, for example.
The output of the software analysis is usually a report containing a large number of tagged errors. However, not all of them are critical. Or rather, the situation usually does not allow for fixing all the defects at once. Therefore, the riskiest vulnerabilities found must be carefully selected for the security team to fix as a priority.
Security audits, such as an operating system security audit, make the work easier. This starts with a simple software check of folder ownership and the detection of tools present. Then it runs the relevant plug-ins and security tests. The second step is a manual analysis from a system administrator’s perspective. At this stage, the most urgent problems are identified in the report. This results in clearly structured guidelines that a security team can then implement. Thus, security audits save much time and work for an internal team.
The Basis Of A Secure System – What Not To Forget
A security upgrade process is network or operating-system-specific. However, its basic structure can be generalised in some ways. So, what security measures should not be ignored?
- Access Restriction – Ensure that access to the infrastructure or system is authenticated physically and virtually. Set up accounts for individuals with different access levels and set only certain rights that correspond to their work. In addition, keep administrative rights to only those absolutely necessary.
- Traffic Filtering and Encryption – Monitoring incoming traffic and its deep filtering with a firewall, and ideally with AntiDDoS protection, should be the basis of every system. Separate the corporate network from the public one and ensure that connections to internal systems are only accessible to employees via a VPN. We also recommend encrypting all traffic and shutting down all unnecessary ports.
- Regular Updates – One of the most common vulnerabilities and opportunities for attackers is outdated applications. Sometimes, it is enough to implement security patches to increase their security; other times, it is necessary to update to a new version. Ensure to follow the recommendations of the publishers of specific software.
- Backups – The demand for backups is already a part of almost every solution. However, it is important to be reminded of them. In addition to the standard regular backups, geo-backups to a second site are also useful in case there are more extensive problems at the primary site.
- System Monitoring – Monitor network traffic, pay attention to anomalies and adjust your security measures accordingly. From time to time, have your system analysed or run penetration tests.
No Time For Hardening And Maintenance? Try Administration
Hardening a system is a never-ending job. It also requires much hard work, and despite all efforts, attackers may still be able to breach the protection. Furthermore, especially smaller companies, but not only them, do not have enough financial and human resources to provide such a high level of security.
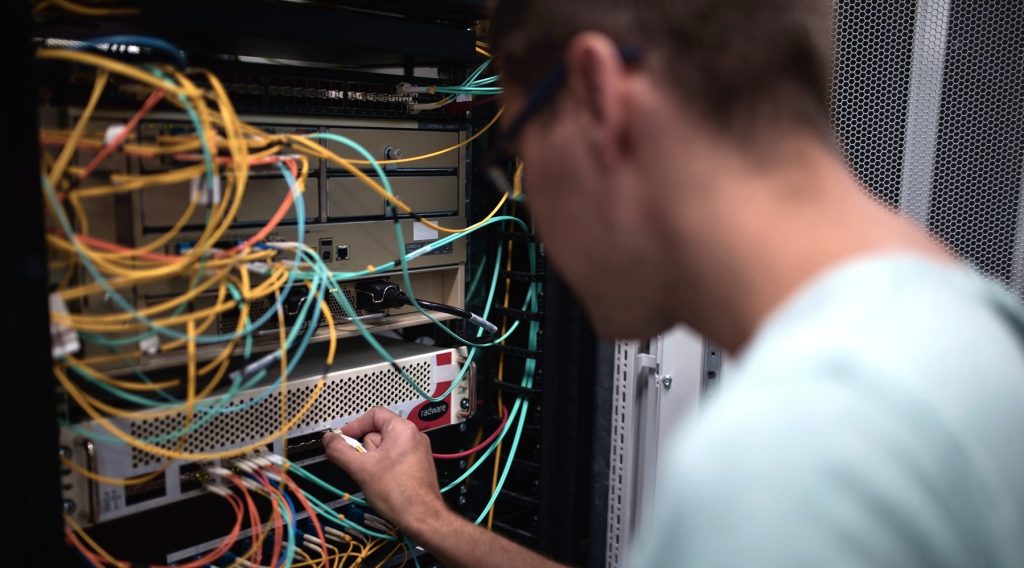
Outsourcing the management of a server or the entire infrastructure will help save time and your employees’ work. In addition, the task of so-called “managed” services is the continuous physical and cybernetic monitoring of a system, as well as the monitoring of updates and their automatic implementation. Another advantage is network connectivity that meets strict security standards or hardware protection against DDoS attacks (at MasterDC, for example, we use Radware DefensePro).